Security Tips: Home Routers
Overview
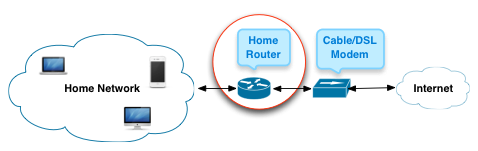
Many Pepperdine faculty and staff are permitted by their supervisors to work from home for part of their scheduled time or perhaps after business hours. This usually means connecting through a home router, across the Internet to the University's network or cloud services. Here are some basic tips for securing your home router.
Prioritized list of security tips
You may need help from your vendor to implement these tips. They're listed in priority order in terms of how much they protect you and your network.
- Don't enable 'remote management' over the Internet. Management is how you configure your router. You should only configure it from inside your home network. Allowing management from the Internet side of your network exposes it to attack from anyone on the Internet. This is usually off by default; check your routers documentation or help website.
- Turn on encryption. Modern routers and laptop/mobile clients support WPA2 aka WPA2 Personal encryption. This is strong encryption based on a shared password and should be used in preference to other encryption options, such as WEP which can be broken.
- Use pass phrases. Have separate pass phrases for your router management and for client devices connecting to your network. These pass phrases should be different; write them down and store them with your private papers. A pass phrase is longer, easier to type and harder to attack. See http://mypassword.pepperdine.edu for pass phrase construction tips. Of course, if your device has default passwords, change them; these are published on lists around the Internet.
- Sign up for updates. Find out from your router manufacturer how to be appraised of updates to the router software. As with computers and mobiles, routers often have software flaws that criminals can exploit. Updates (aka Patches) are used to fix these flaws.
A few other tips and notes
These are not per se security tips but a few things that may help you operate your own network smoothly or things you should know.
- Turn off broadcast for your network name. Anyone trying to attack your network will be able to find it (but not its password, if you have implemented security tips 1-3 above). However, there is some value in not advertising your network in that you'll at least not have neighbors requesting access to your service and people driving by trying to use it. The downside is you have to tell guests the network name and help them find where to type it in on their device. You decide whether this semi-anonymity is worth the trouble.
- Enable a guest network. Some routers provide a 'guest network' with a password you can change frequently while keeping your devices on the main network and not having to change your password on the main network and your family devices after giving a password to guests. Guest networks may also divide your guests from your private network, depending on the features of your router; this provides additional security in case any of your guests are infected.
- Non-IT routers and wireless services are not permitted on any campus network. The Network Engineering department carefully tunes our enterprise routers to provide the best coverage possible. Adding your own wireless network, whether wireless printer or personal router may or may not help you, but almost certainly degrades your colleagues' access -- and also circumvents the University's right and intent to determine who shall access its network. If you have a network connectivity issue, contact the Help Desk.
Final Notes
The security tips above are basic. There are many articles on the web on this subject and some are sensationalist and some are too technical. Whatever other advice you follow, it's important to cover the 4 areas listed above.